Information security
INF028
Use multiple layers of security - 'defence in depth'
Effective security for an information asset can be achieved by using several different layers of security measures.
This approach is referred to as 'defence in depth' — the security of an asset is not significantly reduced with the loss or breach of any single layer of security.
A ‘defence-in-depth’ strategy:
- reduces the likelihood of a successful malicious attack
- minimises the damage that results from an attack.
A simple example is preventing malware from infecting IT systems. You might apply three or more layers of defence:
- a network monitoring and intrusion detection system (IDS)
- an intrusion prevention system (IPS)
- a computer or server anti-malware protection system.
If any one system fails to detect a piece of malware, another system will detect it and prevent the malware from running. It’s important to use a diverse and complementary range of capabilities so each layer can catch and prevent an intrusion that another layer may have missed.
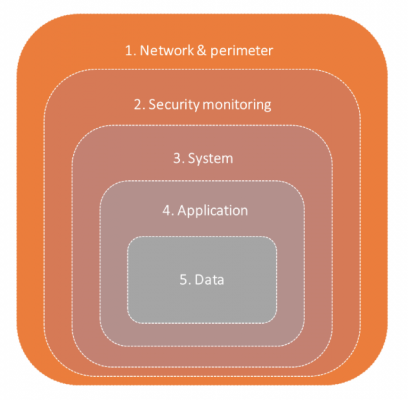
Figure: An example of layers of control in a ‘defence in depth’ information security system in an enterprise environment
Page last modified: 4/05/2022