Information security
INF026
Assess the risks
Once you understand the value of your information and the vulnerabilities and threats you face, assess the risks and identify the appropriate security measures you will adopt. Your risk assessment will inform your decisions about design, certification and accreditation.
During your risk assessment, consult with all relevant people who have insight into the business and security risks that you might face, such as your chief security officer (CSO), chief information security officer (CISO), information security practitioners, and risk owners. The CSO should keep abreast of the organisation’s protective security policy and the threat environment, for robust risk planning and management.
Ensure your security risk management is robust
Organisations should apply sound security risk management practices that follow ISO 31000:2018 and the HB 167/2006 Security risk management.
The Government Chief Digital Officer (GCDO) provides useful guidance on information security and privacy risk management techniques and tools.
Supporting Documents and Information
GCDO Risk Assessment Process: Information Security (PDF, 286KB)
GCDO Risk Assessment Process: Template (Word, 263KB)
GCDO Privacy maturity assessment framework (PDF, 417KB)
Cloud computing — mitigating risk
Prioritise and plan risk mitigations
Once you have defined your risks, prioritise and plan your risk mitigation strategies.
Give high priority to vulnerabilities that may result in the release of private or sensitive information. You can use a simple equation:
- The vulnerability or risk level multiplied by the sensitivity level of the information equals the priority of the vulnerability.
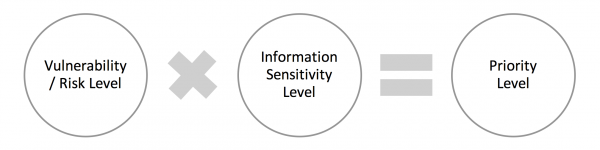
Figure: Vulnerability/Risk prioritisation equation
For example, a high risk vulnerability (such as cross-site scripting or weak password strength) in a standalone system with unclassified information (considered ‘low’ sensitivity) may have a low priority. The same vulnerability in an application that’s linked with others, and that holds citizens’ confidential, financial, or private details may have a ‘high’ priority.
Page last modified: 4/05/2022